- TOP
- Sustainability
- Governance
-
Information Security

Governance
Information Security
Information Security
Information Security Policy
The Hokuriku Electric Industry Group recognizes the protection of information assets as a critical management issue. To secure customer trust and ensure the continuous operation of our business, we establish the following Information Security Policy.
- Purpose
We will ensure the confidentiality, integrity, and availability of information assets and establish a framework with high reliability for information security. - Scope
This policy applies to all employees, officers, and related parties of our Group, as well as all information assets used in business operations. - Compliance
We comply with information security-related laws, regulations, and contracts, including the requirements of ISO/IEC 27001. - Protection of Information Assets
We will manage confidential information, as well as information from business partners such as clients and personal information, based on appropriate and strict rules. - Information Security Measures
We implement multi-layered countermeasures against security risks in information systems to reduce risks. - Responsibilities
All employees and officers understand the importance of information security, comply with this policy and related regulations, and fulfill their responsibilities. To support this, we conduct regular education and training. - Continuous Improvement
We continuously improve our information security management system through regular audits and reviews. - Violation Response
We will respond promptly to any information security violations or incidents and implement measures to prevent recurrence.
Hokuriku Electric Industry Co., Ltd.
President and Representative Director
Ryusho Shimosaka
Information Security Response
The importance of information security measures is increasing to prevent the leakage of our Group’s confidential information, personal information, and other assets, due to increasingly complex cyberattacks and sophisticated unauthorized access. To address such threats and incidents, we strive to minimize the risk of business interruption in our corporate activities, working under the policies of “Strengthening the Protection of Information Assets” and “Ensuring Customer Safety and Security.”
Information Security Framework
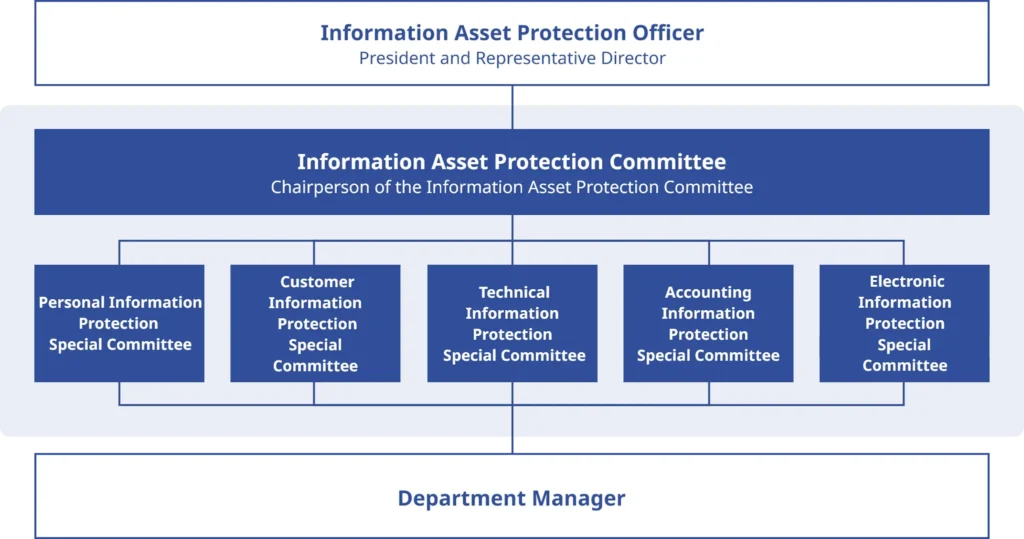
[Organizational Structure]
We have established an “Information Asset Protection Committee” as the organization responsible for deliberating and making decisions on issues and countermeasures related to the overall protection of information assets. This committee is chaired by a director and consists of relevant officers and representatives from each department.
[Information Protection Measures]
To prevent leakage, loss, destruction, falsification, unauthorized access, and other threats to important information assets held and used by our company—including personal information, confidential information (such as customer and technical information, and their electronic data)—we implement appropriate protection and management of information assets through both physical and personnel measures.
Physical Measures
To ensure security against leakage or destruction of information assets, we manage physical access to areas where information assets are stored.
We monitor and control access to areas where personal and confidential information is stored, as well as rooms housing servers and other Information Equipment, striving to prevent unauthorized entry and information leaks.
Risk Countermeasures
To maintain business continuity, respond promptly and appropriately, and achieve rapid recovery in the event of an information security incident, we have established business continuity plans, emergency response systems, and response procedures for anticipated risks. Furthermore, as earthquake countermeasures, we implement disaster prevention measures such as seismic isolation and shock-absorbing devices for Information Equipment.
Human Resources Measures
To ensure compliance with rules regarding the protection of information assets, confidentiality agreements are signed with all executives and employees. Furthermore, we distribute the “Information Security Guide” which summarizes our information management regulations, and conduct regular training and education to enhance security awareness.
| Education | Item | Unit | FY2020 | FY2021 | FY2022 | FY2023 | FY2024 |
| Information Security Education | Number of Sessions | Times | 1 | 2 | 2 | 2 | 2 |
| Participation Rate by Department (Consolidated Basis) |
% | 53.7 | 56.1 | 78.0 | 85.4 | 100.0 |